In a shocking turn of events, an individual recently fell victim to a devastating crypto phishing attack, resulting in the loss of $24 million in digital assets. The stolen cryptocurrencies included 4,851 Rocket Pool ETH (rETH) and 9,579 Lido Staked ETH, making it one of the largest individual crypto phishing incidents to date. Security experts believe the attack was executed through a phishing link, highlighting the critical need for crypto users to be vigilant and proactive in safeguarding their assets.
The Anatomy of the Crypto Phishing Attack
The victim of this massive crypto phishing attack unwittingly authorized a malicious transaction after falling prey to a phishing tactic. Phishing attacks involve deceiving users into signing transactions and interacting with malicious smart contracts.
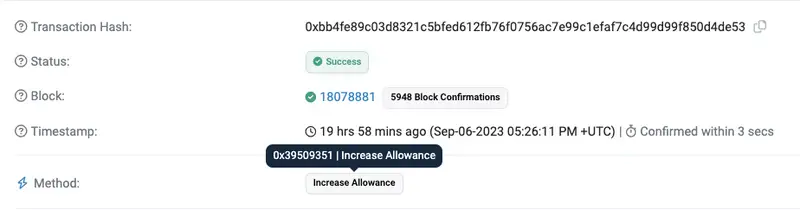
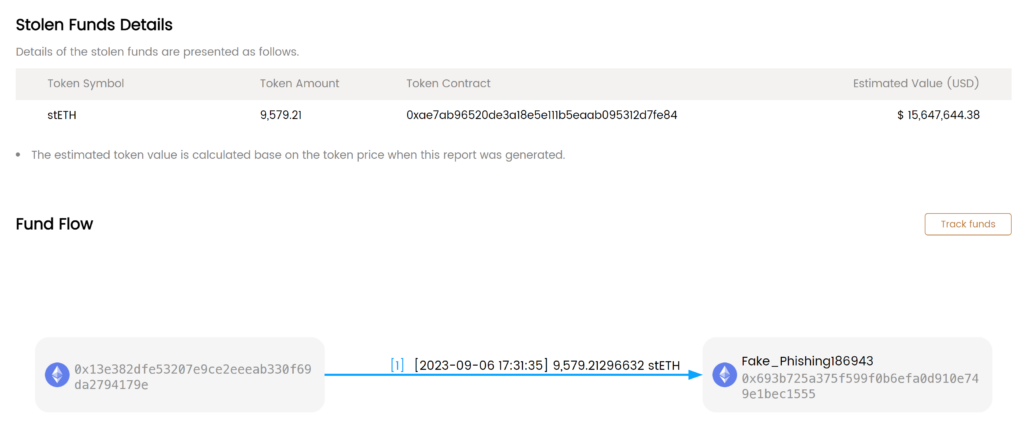
In this case, the funds were stolen using the ‘transferFrom’ function, a transaction that was likely initiated through a phishing link. After interacting with this deceptive link, the victim unintentionally granted the attacker permission to execute the transaction. As a result, the stolen assets were swiftly moved to an address labeled as “Fake_Phishing186943” on the Etherscan block explorer.
Read more: Stake.com Resumes Services After $41M Hack Attempt
The Stolen Assets and Their Fate
The stolen assets in this high-stakes crypto phishing incident comprised 9,579 Lido Staked ETH and 4,851 Rocket Pool ETH. At the time of the attack, these assets were valued at $15.6 million and $8.5 million, respectively, totaling a staggering $24 million. According to Metasleuth, the attacker quickly exchanged the stolen assets for 13,785 Ether (ETH) and 1.64 million Dai (DAI) tokens. Furthermore, a significant portion of the pilfered DAI was transferred to the fully automatic cryptocurrency exchange FixedFloat.
Read more: Terra.money Freezes Website Amid Phishing Scam Concerns
Preventing Similar Losses
The whale’s unfortunate loss serves as a stark reminder of the importance of securing your crypto assets. To avoid falling victim to a phishing attack like this, consider the following tips:
- Limited Spending Permissions: Only approve spending permissions for the exact amount you intend to use. Avoid granting unlimited access to your assets.
- Regularly Check Approved Contracts: Periodically review and revoke permissions for protocols that have been granted unlimited spending or if you have any suspicions. Tools like Revoke Cash and Unrekt can assist with this.
- Verify URLs: Always double-check website addresses before clicking on them. Utilize anti-phishing tools such as Aegis by PeckShield or Wallet Guard to help prevent phishing attacks.
- Separate Wallets: Consider using separate wallets for different purposes, such as holding assets, trading, and participating in airdrops. This segregation can limit potential exposure.
- Practice Due Diligence: Even websites, Discord channels, or Twitter accounts that appear trustworthy can be compromised by hackers. Always conduct your own research (DYOR) and maintain vigilance when engaging in the crypto space.
Conclusion
The recent $24 million crypto phishing attack serves as a stark reminder of the risks associated with the digital asset space. While blockchain technology offers incredible opportunities, it also presents significant security challenges. By implementing the recommended precautions and staying informed about potential threats, crypto users can better protect their investments and contribute to a safer crypto ecosystem. Stay vigilant, and remember that in the crypto world, security should always be a top priority.



![Pionex Review ([currentyear]): Trading Bots, Fees, and Pros & Cons 8 Pionex Review Featured Image](https://coinwire.com/wp-content/uploads/2023/08/pionex-review-featured-image-1024x683.jpg)
![Best Crypto Exchanges in UAE and Dubai to Buy Bitcoin ([currentyear]) 9 Best Crypto Exchanges In Uae And Dubai Featured Image](https://coinwire.com/wp-content/uploads/2024/01/best-crypto-exchanges-in-uae-and-dubai-featured-image-1024x683.jpg)
![Cardano vs Solana ([currentyear]): Is Cardano or Solana better? 10 Cardano Vs Solana Featured Image](https://coinwire.com/wp-content/uploads/2023/06/cardano-vs-solana-featured-image-1024x683.jpg)
![Paybis Review ([currentmonth] [currentyear]): Is It Safe and Legit? 11 Paybis Review Featured Image](https://coinwire.com/wp-content/uploads/2024/05/paybis-review-featured-image-1024x683.jpg)